Difference between revisions of "Generic LDAP Integration"
| [unchecked revision] | [unchecked revision] |
| Line 91: | Line 91: | ||
{{Directory Services Assign Default Privileges}} | {{Directory Services Assign Default Privileges}} | ||
| − | = Configuration Samples | + | == Configuration Samples == |
| − | |||
| − | |||
| + | === Active Directory === | ||
It is possible to connect LDAP Generic to Active Directory, allowing for more flexibility and control than MailStore's built-in Active Directory support. For example, LDAP Generic will allow you to accept invalid or self-signed certificates, use custom filters or change which attributes are used by MailStore. | It is possible to connect LDAP Generic to Active Directory, allowing for more flexibility and control than MailStore's built-in Active Directory support. For example, LDAP Generic will allow you to accept invalid or self-signed certificates, use custom filters or change which attributes are used by MailStore. | ||
| Line 101: | Line 100: | ||
As most Active Directory configurations are quite similar, it will be possible to copy/paste most of the examples below, making only minor modifications based on your environment. | As most Active Directory configurations are quite similar, it will be possible to copy/paste most of the examples below, making only minor modifications based on your environment. | ||
| − | === LDAP Connection === | + | ==== LDAP Connection ==== |
| − | |||
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 133: | Line 131: | ||
|} | |} | ||
| − | === User Filter and Attributes === | + | ==== User Filter and Attributes ==== |
| − | |||
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 179: | Line 176: | ||
|} | |} | ||
| − | === Group Filter and Attributes === | + | ==== Group Filter and Attributes ==== |
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 203: | Line 200: | ||
|} | |} | ||
| − | == OpenLDAP == | + | === OpenLDAP === |
| − | |||
OpenLDAP is a commonly used LDAP server, configuration will require some knowledge of your LDAP environment. | OpenLDAP is a commonly used LDAP server, configuration will require some knowledge of your LDAP environment. | ||
| Line 211: | Line 207: | ||
As OpenLDAP is very flexible, configuration options vary from server to server and you may need to make significant modifications to the examples below to fit the schema used in your environment. | As OpenLDAP is very flexible, configuration options vary from server to server and you may need to make significant modifications to the examples below to fit the schema used in your environment. | ||
| − | === LDAP Connection === | + | ==== LDAP Connection ==== |
| − | |||
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 236: | Line 231: | ||
|} | |} | ||
| − | === User Filter and Attributes === | + | ==== User Filter and Attributes ==== |
| − | |||
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 258: | Line 252: | ||
|} | |} | ||
| − | === Group Filter and Attributes === | + | ==== Group Filter and Attributes ==== |
| − | |||
{| class="wikitable" | {| class="wikitable" | ||
! width=250px | Name | ! width=250px | Name | ||
| Line 288: | Line 281: | ||
{{Directory Services Login with Directory Services Credentials|LDAP server|mads_ldapauth_01.png}} | {{Directory Services Login with Directory Services Credentials|LDAP server|mads_ldapauth_01.png}} | ||
| − | |||
| − | |||
| − | |||
[[de:Generische_LDAP-Integration]] | [[de:Generische_LDAP-Integration]] | ||
[[en:Generic LDAP Integration]] | [[en:Generic LDAP Integration]] | ||
Revision as of 12:56, 25 June 2014
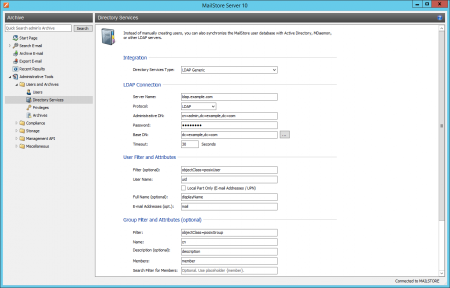
In addition to adding users manually as described in chapter User Management, MailStore Server can synchronize its internal user database with the LDAP server of your organization.
During synchronization, user information, such as user names and email addresses, is copied from the LDAP server into MailStore Server's user database. That way, users can use their LDAP server credentials to also log on to MailStore Server and emails can be assigned to their corresponding user archives automatically, for example. No changes are made to the LDAP server itself by MailStore Server. The scope of the synchronization can be limited through filters.
Accessing Directory Service Integration
- Log on to MailStore Client as a MailStore Server administrator.
- Click on Administrative Tools > Users and Archives > Directory Services.
- In the Integration section, change the directory service type to LDAP server.
Connection to the LDAP Directory Service
For synchronization MailStore Server requires information on how to connect to the LDAP directory service and how to obtain the required data from it.
LDAP Connection
| Name | Description |
|---|---|
| Server Name | DNS name or IP address of your LDAP server |
| Protocol | Configure whether the connection to the LDAP server is to be unencrypted on port 389, LDAP-TLS on port 389, or LDAP-SSL on port 636 |
| Ignore SSL Security Warnings (only when using LDAP-TLS or LDAP-SSL) | Permit connections when a self-signed or non-public certificate is used by the LDAP server |
| Administrative DN | Distinguished Name (DN) or user name of a user with appropriate privileges on the LDAP server |
| Password | Password of the user specified in Administrative DN |
| Base DN | LDAP base DN, if needed |
User Filter and Attributes
| Name | Description |
|---|---|
| Filter (optional) | Filter LDAP objects to return only user objects with email addresses |
| User Name | The LDAP attribute containing the username that you wish MailStore to use |
| Local Part Only (E-mail Addresses / UPN) | If unchecked, MailStore will use the full username including domain portion, e.g. [email protected]. If checked, MailStore will only use the local part of the User Name specified, e.g. the username |
| Full Name (optional) | The full name of the user, for display purposes within MailStore |
| E-mail Addresses (opt.) | The LDAP attribute containing the user's email address. This can contain multiple, comma separated, e-mail addresses |
Group Filter and Attributes
| Name | Description |
|---|---|
| Filter | LDAP filter to return only group objects |
| Name | The LDAP attribute that contains the common name of a group |
| Description (optional) | The LDAP attribute that contains a human readable description for each group |
| Members | The LDAP attribute that contains the common name of group members |
| Search Filter for Members | LDAP filter to resolve group members when members are not specified as a DN string as part of the group results. MailStore will fill in the {member} variable with values from the Members attribute |
| Group | The actual group(s) containing users that MailStore Server will synchronize |
Options
| Name | Description |
|---|---|
| Automatically delete users in MailStore Server | If enabled, MailStore will delete users from the local MailStore database when the user is deleted, removed from the filtered group, or falls out of scope based on the above LDAP filter settings |
Assigning Default Privileges
By default, users that have been synchronized to MailStore Server from a directory service have the privilege to log on to MailStore Server as well as read access to their own user archive.
You can configure those default privileges before synchronization, for example, to assign the privilege Archive E-mail to all new users. To do this, click on Default Privileges...
More information on managing user privileges and their effects is available in the chapter Users, Folders and Settings which also has details on editing existing privileges.
Configuration Samples
Active Directory
It is possible to connect LDAP Generic to Active Directory, allowing for more flexibility and control than MailStore's built-in Active Directory support. For example, LDAP Generic will allow you to accept invalid or self-signed certificates, use custom filters or change which attributes are used by MailStore.
It is assumed that the Active Directory LDAP service is reachable by the MailStore instance on TCP port 389 or 636, including opening ports in the firewall, where applicable.
As most Active Directory configurations are quite similar, it will be possible to copy/paste most of the examples below, making only minor modifications based on your environment.
LDAP Connection
| Name | Description | Example |
|---|---|---|
| Server Name | DNS name or IP address of an Active Directory domain controller. | dc001.example.com |
| Protocol | Active Directory requires encryption | LDAP-TLS or LDAP-SSL |
| Ignore SSL Security Warnings | Active Directory uses self-signed certificates by default. | Checked |
| Administrative DN | Active Directory account for MailStore's use | [email protected] |
| Password | Password of the user specified in Administrative DN above | MySecretPassword |
| Base DN | LDAP base DN will be detected automatically in Active Directory environments | Blank |
User Filter and Attributes
| Name | Description | Example |
|---|---|---|
| Filter (optional) | All users with Exchange e-mail addresses | (&(objectCategory=User)(proxyAddresses=*)) |
| All users with Exchange e-mail addresses who are also listed in the global address book | (&(objectCategory=User)(proxyAddresses=*)(mail=*)) | |
| All users with Active Directory e-mail addresses | (&(objectCategory=User)(mail=*)) | |
| All users | (objectCategory=User) | |
| User Name | Active Directory user name | userPrincipalName |
| NT4 style account name | sAMAccountName | |
| Local Part Only (E-mail Addresses / UPN) | Use the fully qualified username@domain | Unchecked |
| Only use the local part of the User Name | Checked | |
| Full Name (optional) | The user's visible name in Active Directory | displayName |
| E-mail Addresses (opt.) | Exchange environments | proxyAddress |
| Non-Exchange environments |
Group Filter and Attributes
| Name | Example |
|---|---|
| Filter | (objectCategory=Group) |
| Name | cn |
| Description (optional) | description |
| Members | member |
| Search Filter for Members | blank |
| Group | Active Directory Security Group(s) |
OpenLDAP
OpenLDAP is a commonly used LDAP server, configuration will require some knowledge of your LDAP environment.
It is assumed that the LDAP service is reachable by the MailStore instance on TCP port 389 or 636, including opening ports in the firewall, where applicable.
As OpenLDAP is very flexible, configuration options vary from server to server and you may need to make significant modifications to the examples below to fit the schema used in your environment.
LDAP Connection
| Name | Example |
|---|---|
| Server Name | directory.example.com |
| Protocol | LDAP-SSL |
| Ignore SSL Security Warnings | Checked |
| Administrative DN | cn=admin,dc=example,dc=com |
| Password | MySecretPassword |
| Base DN | dc=example,dc=com |
User Filter and Attributes
| Name | Example |
|---|---|
| Filter (optional) | (objectClass=posixAccount) |
| User Name | uid |
| Local Part Only (E-mail Addresses / UPN) | Unchecked |
| Full Name (optional) | displayName |
| E-mail Addresses (opt.) |
Group Filter and Attributes
| Name | Example |
|---|---|
| Filter | (objectClass=posixGroup) |
| Name | cn |
| Description (optional) | description |
| Members | memberUid |
| Search Filter for Members | (|(&(objectClass=posixAccount)(uid={member}))(&(objectClass=posixGroup)(cn={member}))) |
| Group | MailStore Users |
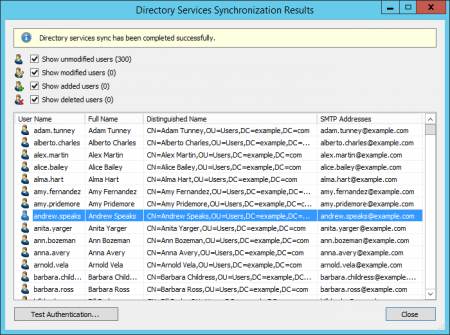
Running Directory Services Synchronization
Click on Test Settings to check synchronization configuration and the results returned by the directory service without any changes to the MailStore Server user database being actually committed.
To finally run the synchronization, click on Synchronize now. The results are shown with any changes committed to the MailStore Server user database.
Login with LDAP server Credentials
After synchronization MailStore users can log on to MailStore Server with their LDAP server username and LDAP server password.