Difference between revisions of "Multi Server Mode Setup"
| [unchecked revision] | [unchecked revision] |
| Line 1: | Line 1: | ||
__NOTOC__ | __NOTOC__ | ||
| − | = Multi Server Mode Setup = | + | == Multi Server Mode Setup == |
| − | |||
When setting up MailStore Service Provider Edition in multi server mode, the first role to set up must always be the Management Server role. Afterwards one or multiple Instance Hosts and Client Access Servers can be set up. Each server in a multi server mode setup can host one or multiple roles. | When setting up MailStore Service Provider Edition in multi server mode, the first role to set up must always be the Management Server role. Afterwards one or multiple Instance Hosts and Client Access Servers can be set up. Each server in a multi server mode setup can host one or multiple roles. | ||
| − | == Set Up Management Server == | + | === Set Up Management Server === |
| − | |||
* If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | * If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | ||
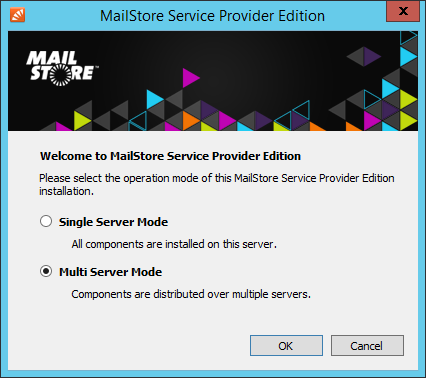
* If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | * If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | ||
| Line 25: | Line 23: | ||
* It is now safe to close the MailStore Service Provider Edition Configuration tool | * It is now safe to close the MailStore Service Provider Edition Configuration tool | ||
| − | == Set Up Instance Host == | + | === Set Up Instance Host === |
| − | |||
* If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | * If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | ||
* If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | * If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | ||
| Line 45: | Line 42: | ||
* It is now safe to close the MailStore Service Provider Edition Configuration tool | * It is now safe to close the MailStore Service Provider Edition Configuration tool | ||
| − | == Set Up Client Access Server == | + | === Set Up Client Access Server === |
| − | |||
* If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | * If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: <tt>%PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe</tt>. | ||
* If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | * If no configuration files and services are found, the ''MailStore Service Provider Edition Configuration'' will ask for the desired mode. Select ''Multi Server Mode'' and click ''OK''. | ||
| Line 74: | Line 70: | ||
* It is now safe to close the MailStore Service Provider Edition Configuration tool | * It is now safe to close the MailStore Service Provider Edition Configuration tool | ||
| − | == Pairing with Management Server == | + | === Pairing with Management Server === |
| − | |||
Before Client Access Servers and Instance Hosts are able to communicate with the Management Server, SSL certificate fingerprints must be exchanged to establish a trust relationship. Additionally the Instance Hosts and Client Access Servers must be registered in the Management Server with its server name and TCP port. | Before Client Access Servers and Instance Hosts are able to communicate with the Management Server, SSL certificate fingerprints must be exchanged to establish a trust relationship. Additionally the Instance Hosts and Client Access Servers must be registered in the Management Server with its server name and TCP port. | ||
| Line 89: | Line 84: | ||
If your security policy does not permit establishing such a connection, pairing must be performed manually. Please refer to [[Management Console - Infrastructure#Add New Instance Host|Add New Instance Host]] or [[Management Console - Infrastructure#Add New Client Access Server|Add New Client Access Server]] for further details. | If your security policy does not permit establishing such a connection, pairing must be performed manually. Please refer to [[Management Console - Infrastructure#Add New Instance Host|Add New Instance Host]] or [[Management Console - Infrastructure#Add New Client Access Server|Add New Client Access Server]] for further details. | ||
| − | = What to do next = | + | == What to do next == |
| − | |||
In production environments it is recommended to replace the self-signed certificates used by the Client Access Server's IMAP and HTTP server with certificates signed by a trusted root certificate authority. Further details can be found in [[Replace Self-signed SSL Certificates]] | In production environments it is recommended to replace the self-signed certificates used by the Client Access Server's IMAP and HTTP server with certificates signed by a trusted root certificate authority. Further details can be found in [[Replace Self-signed SSL Certificates]] | ||
Revision as of 10:37, 1 July 2014
Multi Server Mode Setup
When setting up MailStore Service Provider Edition in multi server mode, the first role to set up must always be the Management Server role. Afterwards one or multiple Instance Hosts and Client Access Servers can be set up. Each server in a multi server mode setup can host one or multiple roles.
Set Up Management Server
- If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: %PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe.
- If no configuration files and services are found, the MailStore Service Provider Edition Configuration will ask for the desired mode. Select Multi Server Mode and click OK.
- Click Add Server Role
- Select Management Server
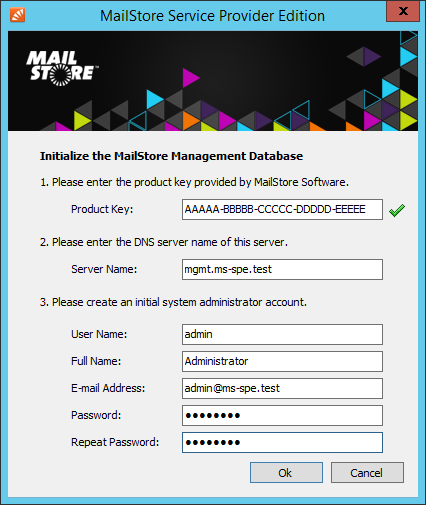
- Enter your product key into the Product Key field and change Server Name to the fully qualified host name of the server (e.g. mgmt.ms-spe.test). Finally enter and confirm the admin password that will be used to log on to the Management Console.
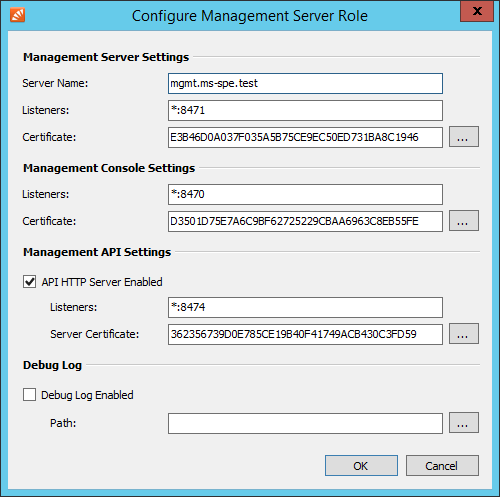
- Fill out the Configure Management Server Role form.
- Server Name: Fully qualified host name (FQHN) of the server
- TCP Server Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections from the Management Server (Default: *:8471)
- TCP Server Certificate: Fingerprint of the SSL certificate used by the Management Server to authenticate against Instance Hosts and Client Access Serves. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- HTTP Server Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections to the Management Console and Management API (Default: *:8470)
- HTTP Server Certificate: Fingerprint of the SSL certificate used by the Management Server's HTTP server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- Click OK to add the Management Server role.
- Click 'Start to start the Management Server service.
- 'Please note: As the startup process of the services is asynchronous, please wait up to 30 seconds. A service shown as running may still switch back to stopped during that period if an error occurred.
- It is now safe to close the MailStore Service Provider Edition Configuration tool
Set Up Instance Host
- If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: %PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe.
- If no configuration files and services are found, the MailStore Service Provider Edition Configuration will ask for the desired mode. Select Multi Server Mode and click OK.
- Click Add Server Role
- Select Instance Host
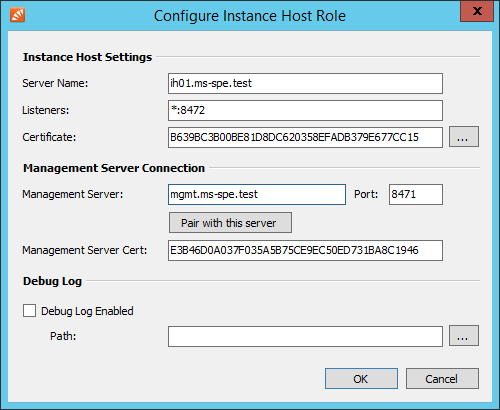
- Fill out the Configure Instance Host Role form.
- Server Name: Fully qualified host name (FQHN) of the server
- TCP Server Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections from the Management Server (Default: *:8472)
- TCP Server Certificate: Fingerprint of the SSL certificate used by the Instance Host to authenticate against Management Server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- Management Server: Fully qualified host name (FQHN) of the Management Server to connect to.
- Port: TCP port where the above Management Server accepts incoming connections.
- Management Server Cert Fingerprint of the SSL certificate used by the Management Server to authenticate against Instance Host. This value is set automatically when Pairing with Management Server
- Click OK to add the Instance Host role.
- Click 'Start to start the Instance Host service.
- 'Please note: As the startup process of the services is asynchronous, please wait up to 30 seconds. A service shown as running may still switch back to stopped during that period if an error occurred.
- It is now safe to close the MailStore Service Provider Edition Configuration tool
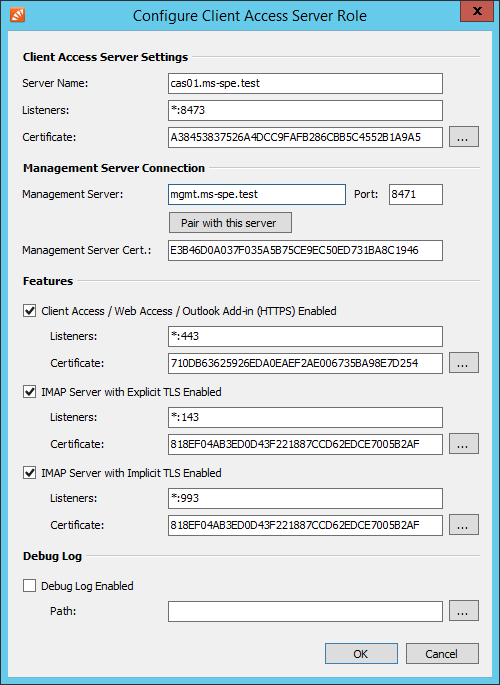
Set Up Client Access Server
- If not executed automatically by the installation program, start the MailStore Service Provider Edition Configuration tool by double-clicking its desktop icon. On a Windows Server Core use the command line prompt to start the executable (default: %PROGRAMFILES%\MailStore Infrastructure\MailStoreInfrastructureConfig.exe.
- If no configuration files and services are found, the MailStore Service Provider Edition Configuration will ask for the desired mode. Select Multi Server Mode and click OK.
- Click Add Server Role .
- Select Client Access Server.
- Fill out the Configure Client Access Server Role form.
- Server Name: Fully qualified host name (FQHN) of the server
- TCP Server Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections from the Management Server (Default: *:8473)
- TCP Server Certificate: Fingerprint of the SSL certificate used by the Client Access Server to authenticate against Management Server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- Management Server: Fully qualified host name (FQHN) of the Management Server to connect to.
- Port: TCP port where the above Management Server accepts incoming connections.
- Management Server Cert Fingerprint of the SSL certificate used by the Management Server to authenticate against Client Access Server. This value is set automatically when Pairing with Management Server
- HTTP Server Enabled: If enabled the Client Access Server provides access to archives via MailStore Client, MailStore Outlook Add-in and MailStore Web Access.
- Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections (Default: *:443)
- Server Certificate: Fingerprint of the SSL certificate used by the HTTP Server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- IMAP Server with explicit TLS Enabled: If enabled the Client Access Server provides access to archives via IMAP protocol. Connection can either be unencrypted or secured via STARTTLS.
- Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections (Default: *:143)
- Server Certificate: Fingerprint of the SSL certificate used by the IMAP Server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- IMAP Server with implicit TLS Enabled: If enabled the Client Access Server provides access to archives via IMAP protocol. Connection is encrypted via SSL/TLS.
- Listeners: If the server is multihomed you can specify on which IP address and TCP port to listen for incoming connections (Default: *:993)
- Server Certificate: Fingerprint of the SSL certificate used by the IMAP Server. Use the button next to the fingerprint to select a different certificate from the computer's certificate store.
- Click OK to add the Client Access Server role.
- Click 'Start to start the Client Access Server service.
- 'Please note: As the startup process of the services is asynchronous, please wait up to 30 seconds. A service shown as running may still switch back to stopped during that period if an error occurred.
- It is now safe to close the MailStore Service Provider Edition Configuration tool
Pairing with Management Server
Before Client Access Servers and Instance Hosts are able to communicate with the Management Server, SSL certificate fingerprints must be exchanged to establish a trust relationship. Additionally the Instance Hosts and Client Access Servers must be registered in the Management Server with its server name and TCP port.
This process can simply be performed by using the pairing function as described in the following:
- Enter the fully qualified host name of the Management Server in the corresponding field while configuring an Instance Host or Client Access Server.
- Click Pair with this server.
- Enter the user name and password of a MailStore Service Provider Edition administrator.
- Click OK to pair with Management Server
Please note: Pairing is carried out through the Management API. Therefore the Instance Hosts and Client Access Servers must be able to establish a connection to the HTTP server on the Management Server (Default TCP port: 8470).
If your security policy does not permit establishing such a connection, pairing must be performed manually. Please refer to Add New Instance Host or Add New Client Access Server for further details.
What to do next
In production environments it is recommended to replace the self-signed certificates used by the Client Access Server's IMAP and HTTP server with certificates signed by a trusted root certificate authority. Further details can be found in Replace Self-signed SSL Certificates